Enrolling Devices.
One of the advantages of deploying Chromebooks into schools is the ease of management. With no dependency on local infrastructure and a simple to use web management console, installing and configuring Chromebooks couldn’t be more straightforward.
Wouldn’t it be great if your Windows devices worked in the same way? Well with Microsoft’s new SaaS based framework maybe they can.
In this series of posts I take a look at Windows Modern Management from the point of view of the Chromebook administrator and just to make it interesting lets jumble things up a bit and assume Chromebooks are the established technology.
In this alternative reality Microsoft Windows is the new kid on the block and you have the job of incorporating this feisty newcomer into your serverless SaaS based school? So let's take the red pill and wander around this particular wonderland just to see how far we can go.

Windows Version.
Fortunately our imaginary school has invested in a batch of Windows 10 laptops all running the 1809 feature update. You can try this trick on your IT suite running Windows 8 but I suspect you won’t get very far. After all you wouldn’t expect a set of Chromebooks running version 55 to support all the functions of admin console and Windows is no different. So the first step is to make sure you have the latest Windows 10 release.
User Accounts.
Currently Windows devices only authenticate through a Microsoft user directory. So as much as the Chromebook admin would like to see a Google dialog logon on boot that’s not going to happen soon.
Note: Since this post was written this has become possible. Details are given here.
For this reason all your users will need a Windows Azure account to control the access rights and licensing. This really shouldn’t be a surprise because all SaaS services work by referencing some form of local account even if authentication is managed by another party. Although you can force Chromebooks to use Azure AD as an authentication source you still have to maintain a separate Google user account to apply policy.
Web Management.
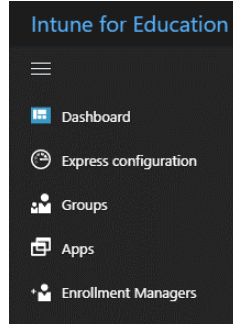
Google provides a web based management console that controls all aspects of the User and Device policy for Chromebooks. Microsoft's counterpart is the InTune for Education portal. The first thing any G Suite administrator will notice moving into Microsoft’s wonderland is the fact that many of the management functions are split between various web portals, all having different navigation styles and UI layouts.
The InTune for Education portal is itself a simplified ‘skin’ that rest on top of the InTune blade in the Azure console. In this walkthrough we’ll stick with InTune for Education unless we’re forced out for some function. Right on cue the first one of these is user and licence assignment which is not managed by InTune for Education but the Office365 portal.
For the records the Windows Administrator will be spending most of the time moving between the following portals.
Office 365 - User management and Licencing
InTune for Education - General Device Management
Azure Portal - Advanced Device Management
Microsoft Store for Education - Application selection and authorization.
Licencing.
Licencing Chromebooks is easy. It’s a one-off device licence that’s valid for the life of the Chromebook. This simple relationship has not been lost on Microsoft and they have a direct equivalent, an InTune device licence that lasts for five years. The cost is roughly equivalent and it gives you the ability to apply policy to the device and any organisational user account logging onto the same PC/laptop. It’s a very good deal and highly recommended.
Unfortunately that’s the end of the good news because although the device licence exists and can be purchased there’s no way of applying it to a device. It’s almost like the licence has been released to meet a marketing need before the software exists to support it. No doubt this will be fixed in time but currently the failback is to apply inTune license to individual user accounts and that’s done though the Office365 portal.
Enrolment and DEM accounts..
We now have user accounts set up in Azure and InTune licences applied to those accounts so lets start enrolling some devices. Google admins will be familiar with the fact that enrolling Chromebook out of the box is pretty easy and an small cottage industry has grown up to support the mass deployment of Chromebooks. In comparison the InTune enrolment experience takes a bit longer but on the whole is pretty slick and surprisingly straightforward.
Microsoft have a new facility called AutoPilot which we don’t cover here. It’s the equivalent of a Chromebook white-glove service working through the partner channels.
The first thing you will need is a device enrolment manager (DEM) account. Unlike G Suite where any user account can enroll a Chromebook, you need a user account with a special deployment flag set to enroll devices in bulk. Once created and with an InTune user licence applied you can enroll up to one thousand mobile devices using a single DEM account. The InTune for Education portal provides simple dialog to create and manage Azure enrolment accounts.
Once we have our DEM account created we are ready to enroll.
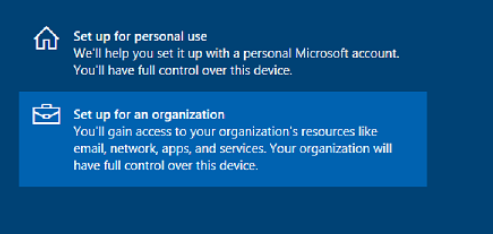
Power on your new Windows 10 device and move through the OOBE inputs. Set any dialogs regarding language and network access and select Set up for an organisation which is the the Windows equivalent of Ctrl -Alt-E.
Signing in using the DEM account adds the device to the Azure directory and places it under InTune management. Once rebooted you can logon using any organisational account with both device and user policies applied. Pretty simple.
Opening the InTune for Education portal you’ll see the appliance listed in the All Devices section along with some basic system information. The managed by field should read MDM.

The check in time records the last time the device took policy from Azure. A sync can be forced at any time and is a useful way of getting changes out to the devices on a short schedule. The time taken to apply a policy update can vary from seconds to a long coffee break so the ability to force a sync is a useful tool.
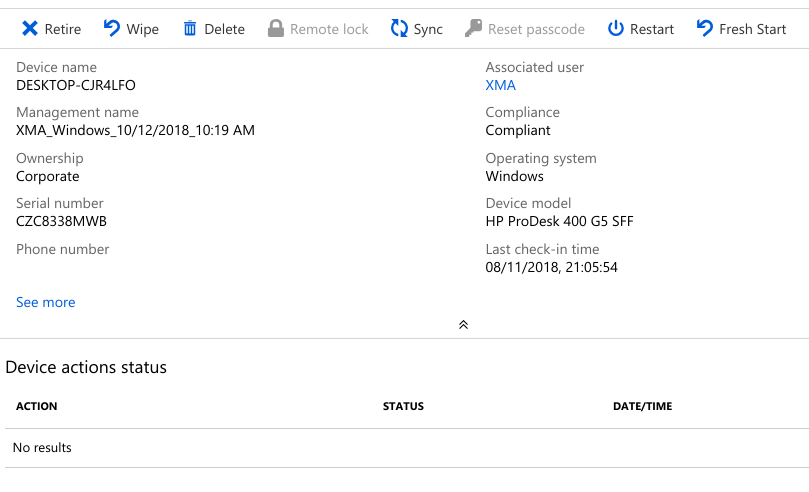
Opening the device record displays further information and options that would be familiar to the the Chromebook manager. The Retire action is the equivalent of deprovisioning in Chrome with one major difference, the licence is returned to the pool. The admin also has the option to force a restart of the device, wipe the PC of personal data and return to factory default settings - a sort of remote Esc-Refresh-Power.
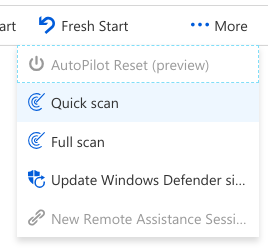
Hidden under the More button are actions to force a virus scan of the device and update Windows defender, duties that the Chromebook admin doesn't have worry about but essential tasks for the Windows admin.
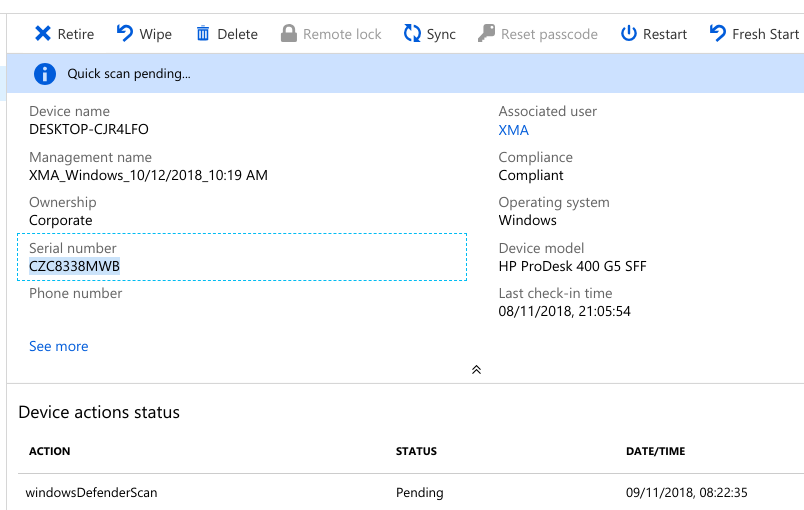
The device action panel records the status and result of all active tasks.
Now we have the device enrolled we can take a look at policy management in the next post.
Next: InTune for Chromebook Admins (p2).
Also: Windows Delivery Optimisation for the G Suite admin.
One of the advantages of deploying Chromebooks into schools is the ease of management. With no dependency on local infrastructure and a simple to use web management console, installing and configuring Chromebooks couldn’t be more straightforward.
Wouldn’t it be great if your Windows devices worked in the same way? Well with Microsoft’s new SaaS based framework maybe they can.
In this series of posts I take a look at Windows Modern Management from the point of view of the Chromebook administrator and just to make it interesting lets jumble things up a bit and assume Chromebooks are the established technology.
In this alternative reality Microsoft Windows is the new kid on the block and you have the job of incorporating this feisty newcomer into your serverless SaaS based school? So let's take the red pill and wander around this particular wonderland just to see how far we can go.
Windows Version.
Fortunately our imaginary school has invested in a batch of Windows 10 laptops all running the 1809 feature update. You can try this trick on your IT suite running Windows 8 but I suspect you won’t get very far. After all you wouldn’t expect a set of Chromebooks running version 55 to support all the functions of admin console and Windows is no different. So the first step is to make sure you have the latest Windows 10 release.
User Accounts.
Currently Windows devices only authenticate through a Microsoft user directory. So as much as the Chromebook admin would like to see a Google dialog logon on boot that’s not going to happen soon.
Note: Since this post was written this has become possible. Details are given here.
For this reason all your users will need a Windows Azure account to control the access rights and licensing. This really shouldn’t be a surprise because all SaaS services work by referencing some form of local account even if authentication is managed by another party. Although you can force Chromebooks to use Azure AD as an authentication source you still have to maintain a separate Google user account to apply policy.
Web Management.
Google provides a web based management console that controls all aspects of the User and Device policy for Chromebooks. Microsoft's counterpart is the InTune for Education portal. The first thing any G Suite administrator will notice moving into Microsoft’s wonderland is the fact that many of the management functions are split between various web portals, all having different navigation styles and UI layouts.
The InTune for Education portal is itself a simplified ‘skin’ that rest on top of the InTune blade in the Azure console. In this walkthrough we’ll stick with InTune for Education unless we’re forced out for some function. Right on cue the first one of these is user and licence assignment which is not managed by InTune for Education but the Office365 portal.
For the records the Windows Administrator will be spending most of the time moving between the following portals.
Office 365 - User management and Licencing
InTune for Education - General Device Management
Azure Portal - Advanced Device Management
Microsoft Store for Education - Application selection and authorization.
Licencing.
Licencing Chromebooks is easy. It’s a one-off device licence that’s valid for the life of the Chromebook. This simple relationship has not been lost on Microsoft and they have a direct equivalent, an InTune device licence that lasts for five years. The cost is roughly equivalent and it gives you the ability to apply policy to the device and any organisational user account logging onto the same PC/laptop. It’s a very good deal and highly recommended.
Unfortunately that’s the end of the good news because although the device licence exists and can be purchased there’s no way of applying it to a device. It’s almost like the licence has been released to meet a marketing need before the software exists to support it. No doubt this will be fixed in time but currently the failback is to apply inTune license to individual user accounts and that’s done though the Office365 portal.
Enrolment and DEM accounts..
We now have user accounts set up in Azure and InTune licences applied to those accounts so lets start enrolling some devices. Google admins will be familiar with the fact that enrolling Chromebook out of the box is pretty easy and an small cottage industry has grown up to support the mass deployment of Chromebooks. In comparison the InTune enrolment experience takes a bit longer but on the whole is pretty slick and surprisingly straightforward.
Microsoft have a new facility called AutoPilot which we don’t cover here. It’s the equivalent of a Chromebook white-glove service working through the partner channels.
The first thing you will need is a device enrolment manager (DEM) account. Unlike G Suite where any user account can enroll a Chromebook, you need a user account with a special deployment flag set to enroll devices in bulk. Once created and with an InTune user licence applied you can enroll up to one thousand mobile devices using a single DEM account. The InTune for Education portal provides simple dialog to create and manage Azure enrolment accounts.
Power on your new Windows 10 device and move through the OOBE inputs. Set any dialogs regarding language and network access and select Set up for an organisation which is the the Windows equivalent of Ctrl -Alt-E.
Signing in using the DEM account adds the device to the Azure directory and places it under InTune management. Once rebooted you can logon using any organisational account with both device and user policies applied. Pretty simple.
Opening the InTune for Education portal you’ll see the appliance listed in the All Devices section along with some basic system information. The managed by field should read MDM.
The check in time records the last time the device took policy from Azure. A sync can be forced at any time and is a useful way of getting changes out to the devices on a short schedule. The time taken to apply a policy update can vary from seconds to a long coffee break so the ability to force a sync is a useful tool.
Opening the device record displays further information and options that would be familiar to the the Chromebook manager. The Retire action is the equivalent of deprovisioning in Chrome with one major difference, the licence is returned to the pool. The admin also has the option to force a restart of the device, wipe the PC of personal data and return to factory default settings - a sort of remote Esc-Refresh-Power.
Hidden under the More button are actions to force a virus scan of the device and update Windows defender, duties that the Chromebook admin doesn't have worry about but essential tasks for the Windows admin.
The device action panel records the status and result of all active tasks.
Now we have the device enrolled we can take a look at policy management in the next post.
Next: InTune for Chromebook Admins (p2).
Also: Windows Delivery Optimisation for the G Suite admin.









